Furthermore, the authentication strategy based on smart contracts is combined with Mobile Edge Computing (MEC) to realize access control of users …
http://dlvr.it/TJ70DX
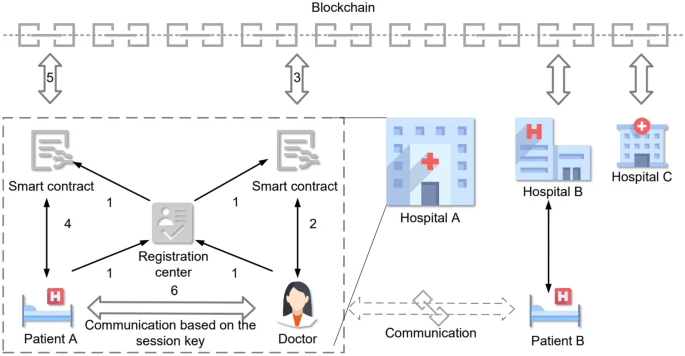
Provably secure and lightweight blockchain based cross hospital authentication scheme for …
Written in
by
Tags
Leave a comment