Boopathi et al. propose a strategy to improve edge computing data privacy by utilizing secure transfer, DL optimization, and trust-based encryption …
http://dlvr.it/THbqrh
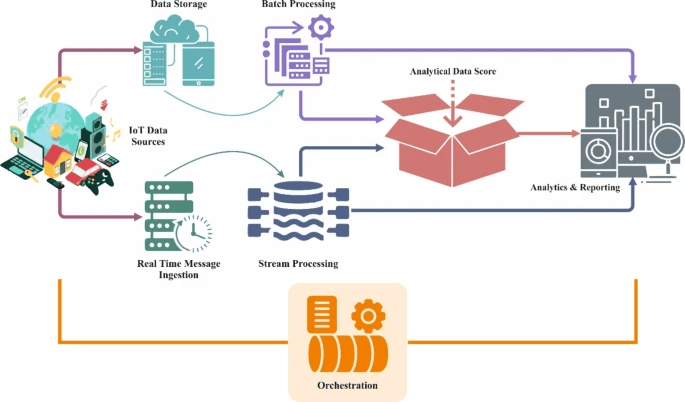
Privacy-preserving approach for IoT networks using statistical learning with optimization …
Written in
by
Tags
Leave a comment